Bwapp Login Password Apr 2026
Also, include a moral compass—emphasize that this is for educational purposes and that performing such attacks on real systems is illegal.
Need to check if there are any standard username/password combos for BWAPP. From what I remember, the default is "admin / admin" or other user accounts for testing. But maybe the story can involve a scenario where the user is supposed to find out the password using the SQL injection method. However, in the story, the character should be doing this in a legal, educational setting.
I should also include step-by-step actions the character takes. Maybe they first try logging in with a default password, which fails, then realize they need to exploit a SQL injection vulnerability. The story could explain the technique in simple terms without being too technical, but enough to show the process. The climax could be the successful authentication through the exploitation, followed by a lesson on how to secure the login. bwapp login password
I need to make sure the story is clear and follows a logical flow. Start with the setup, the character's motivation, the problem they face, their approach to solving it (with ethical considerations), and the conclusion with learning outcomes. Avoid glorifying hacking; instead, emphasize the educational aspect.
Make sure the story doesn't provide a real password or method that can be misused. Instead, it should guide the reader through a hypothetical scenario focusing on understanding the vulnerability. Also, include a moral compass—emphasize that this is
In a dimly-lit university lab, cybersecurity student Maya sat hunched over her laptop, her fingers flying across the keyboard. Before her loomed a challenge: the infamous puzzle, a notorious part of Ben's Web Application Attacking Project. BWAPP was a sandbox of vulnerabilities, designed for ethical hackers to practice identifying and mitigating exploits. For Maya, it was a rite of passage. Set Up: The Educational Sandbox BWAPP was no ordinary tool—it was a virtual lab where instructors taught students about SQL injection, XSS, and other critical security flaws. The login screen glared at Maya, demanding credentials. She knew the default username was "admin," but the password was a mystery. "If this were a real system," she reminded herself, "this would be illegal. But here? It's a lesson in how not to build software." The Challenge: Bypassing the Login Maya tried the obvious: "admin:admin," "guest:guest," even "password." No luck. The application was mocking her. Frustrated, she opened her browser's developer tools, recalling her lecture on input validation flaws . "What if the password field is vulnerable to SQL injection?" she thought. She entered a test input: admin' OR '1'='1 . The login failed, but the error message whispered hope: "Invalid username or password." No trace of a SQL error—subtle, but promising. The Exploit: Bypassing Security with Code Maya refined her approach. She crafted a payload to test if the backend was filtering inputs properly. She typed:
I need to ensure the story is educational and highlights the importance of secure practices. Maybe the protagonist uses the SQL injection to test the system, then reports the vulnerability. Alternatively, they might learn about the vulnerability and how to prevent it. But maybe the story can involve a scenario
Okay, with that outline, I can start drafting the story, ensuring it meets these points and provides a proper narrative.
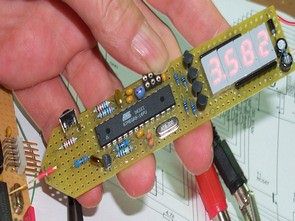


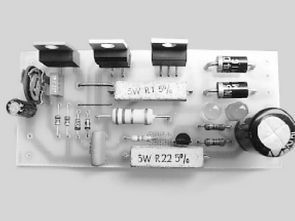
PIC16F84 RF Transceiver Circuit (6-Channel)
As the first state of the circuit, when a button is pressed that button button corresponding LED lights up when he left, but did not go out, ta else until you press a button. So was continuously in one LED always stays on.
As the logic in the program only when the buttons are pushed, the data were sent information. I additionally buttons and while holding both pressed when it is not data information, sending buttons while pressing the corresponding LED burning when you left it (I’ve added the command here comes into play.), Extinguishing’ve made.
RF Transceiver Schematic